Contact numbers:
+964 773 157 0666
+964 751 886 5258
+964 780 002 5353
Contact numbers:
+964 773 157 0666
+964 751 886 5258
+964 780 002 5353

Email has been around for a long time now. But it’s changed
very little, and remains a pivotal business tool and a communication mechanism
that’s:
The rise of social engineering: tricks used
to fool the user.
Social engineering can take a number of forms and can be
applied to different media. Phishing: when an attacker, masquerading as a
trusted entity, dupes a victim into the opening and acting on an email, instant
message, or text message remains the most common. Its more sophisticated
subset, spear-phishing, focuses on a specific individual, organization, or
business. The aim in all cases is to persuade the recipient to either:
Clearly, email recipients will only undertake any of these
actions (in theory, at least) if they’re confident that this is a legitimate
request. They need to trust the sender, or at least recognize the sender’s
authority. You can learn more about other social engineering forms in this
blog.
The credible
sender
So, the fraudulent sender needs to look like the real thing. They need to ‘spoof’ to represent themselves as a named sender who the recipient naturally trusts, or a domain name the sender thinks they recognize and are reassured by.
Let's start with how to spoof a domain name: a ‘cousin’ domain looks almost exactly like the domain name the recipient expects to see. And because we expect to see something, we can easily overlook the tiny difference responsible for that ‘almost exactly’.
Briefly, [email protected] looks pretty much the same as [email protected] - the addition or replacement of one character may be the sole difference between the address of your regular supplier and that of your attacker.
Or look at this: your email from [email protected] comes through as from [email protected]. Again, this completely different domain address is designed to fool you into trusting the apparently familiar sender.
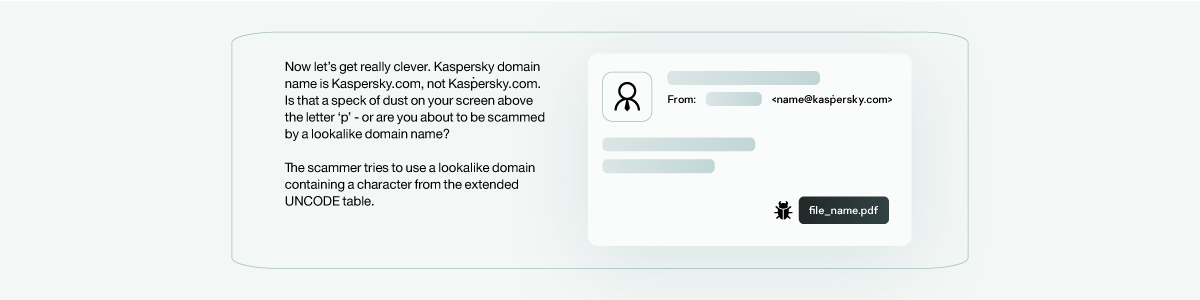
And it can be even more subtle than this!
Some characters from the extended UNICODE charset, like the Cyrillic letters ‘с’ ‘р’ or ‘e’ - look exactly like those from the historical ASCII set still used by the Domain Name System (DNS).
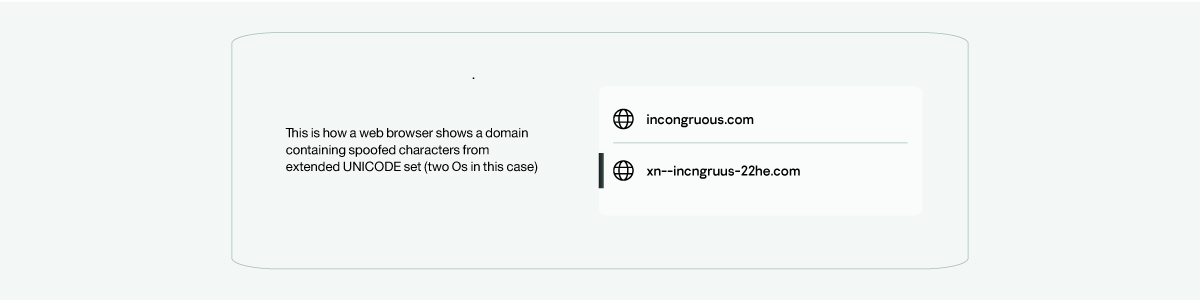
For example, domain name “incongruous.com” as first seen in the illustration below in fact contains two Os from the Cyrillic UNICODE symbol range – which of course you didn’t spot. The DNS system, using the so-called ‘Punycode’ method, would see it as “xn-- incngruus-22he.com” but the email client would display it just as we see it here. This is a hard trick for a recipient to see through.
All we can say is that if you have the faintest suspicion about an email, try copying the domain name into the address string of an internet browser, Chrome, Edge or Internet Explorer will do the trick, though not Firefox. The browser will show the string in ASCII format, and if there are any extended UNICODE characters lurking there you’ll see it at once.
And you are?
A ‘cousin’ domain looks almost exactly like the domain name the recipient expects to see. And because we expect to see something, we can easily overlook the tiny difference responsible for that ‘almost exactly’.
The fact is, anyone can call themselves anything when sending an email.
Under ‘From’ on your Outlook Inbox page, you see a name followed by the first
line of the email text, but not the email address of the sender. At the head of
the email, you see the ‘From’ name followed by their email address <in
brackets>. Email providers include the facility for you to call yourself
anything you want as an email sender: your own name, your dog’s name, or if
you’re a scammer, the name of the boss of the person you’re currently engaged
in spear-phishing.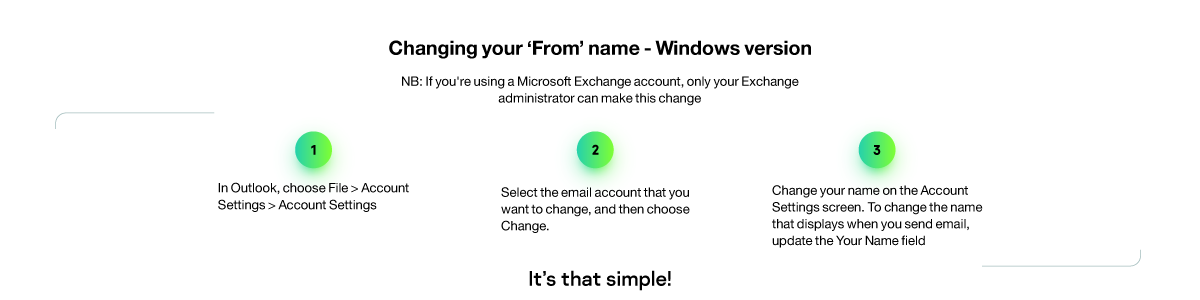
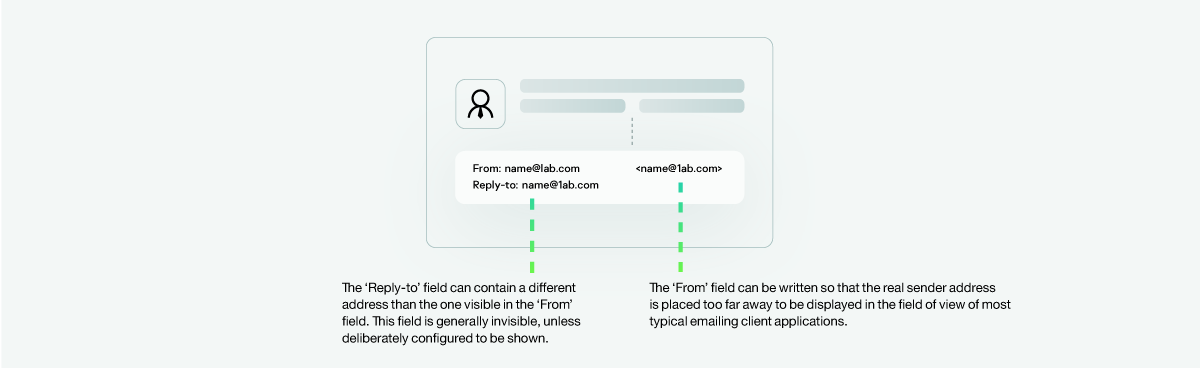
Or how about this? you make your ‘From’ name the legitimate
email address you’re impersonating. So, you send your fraudulent email from
your fraudulent [email protected] address, but the recipients ‘From’
field will initially read ‘Invoicing@Incongruous. com’ (the correct address,
although in plain text).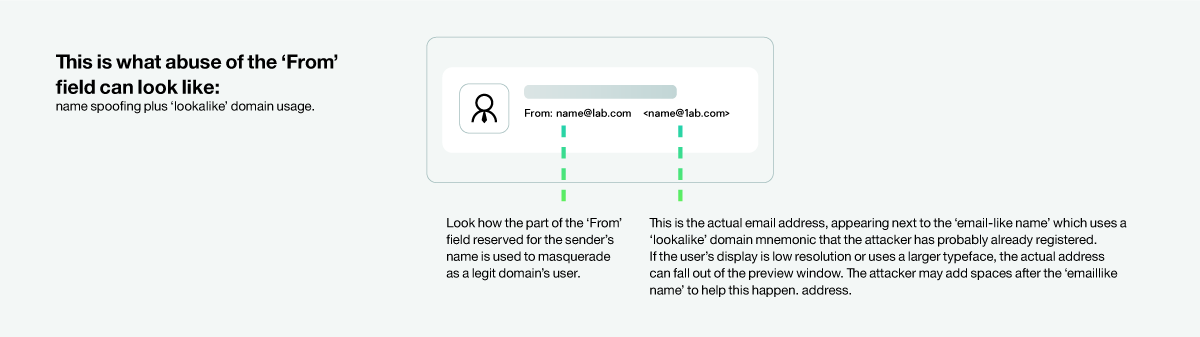
Next, there’s the fact that the sender of an email is not necessarily the recipient of your response. Email services also provide the facility to include a completely different address from that of the sender, to which the email response is automatically sent.
This is a valuable tool if, for example, you’re
sending an email from your CEO, but responses will be handled by a team rather
than the CEO personally, so you want these to go straight to the team. It’s
also useful for scammers, particularly as the different response address is not
shown anywhere on the recipient’s screen.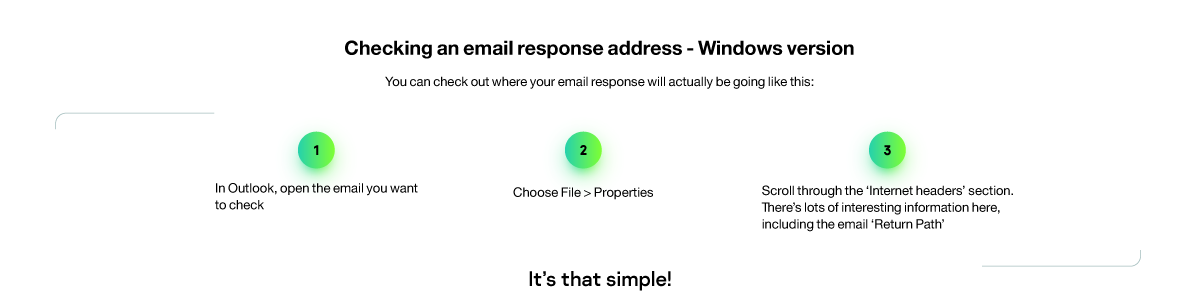
If you look into the message header, a number of the attacker’s tricks become apparent.
We’ve touched on one answer to many of the social engineering tricks described here. Of course, the whole point of these fraudulent emails is that they look credible, so vigilance would suggest manually checking and rechecking the email address and header properties of every email, however genuine the sender might appear. Which is never going to happen.
The contents of the email itself will dictate whether it particularly warrants this level of investigation. ‘Why are our auditors suddenly sending us this document? And am I even 100% sure this email is really from them?’ ‘Why does Jake need me to send him these confidential customer files? Can’t he access them himself? And why’s he using his home email address?’
User awareness is key. There needs to be a continuous process of raising
and maintaining user awareness through whatever means are available, including
ongoing education and training. 
How do we define an effective email security solution?
Gateway level protection: first, the security solution needs to prevent fraudulent emails from ever reaching an endpoint where possible, so the user is never exposed to them. For the majority of all email threats, this can be achieved at the gateway level. The fraudulent email is spotted due to the nature of its contents, its links and/or its attachments, and other machine-logic-based criteria, together with mail authentication techniques, etc. and blocked before it can get anywhere near its target.
Mailbox-level protection: regardless of the quality of your gateway-level defenses, you’re going to need equally intelligent protection that can recognize and block those more sophisticated phishing and malware-carrying emails designed to circumvent (or never even cross paths with) email security gateways. The solution you’re about to choose must be able to keep watch over ‘horizontal’ or intra-corporate emails and re-check those already in people's mailboxes. ‘Intelligent’ here means having continuous access to sources of the latest and most reliable security threat intelligence (TI) together with machine learning (ML) and applied linguistics-based technologies.
Advanced content filtering: social engineering-based phishing and spear-phishing are not of course the only forms of attack. Data-stealing or simply maliciously destructive malware, ubiquitous ransomware, and Advanced Persistent Threats or APTs are just some of the forms of threat that require detection and elimination. by analyzing and neutralizing suspect emails, perhaps by removing a suspicious attachment, or by blocking them entirely. ‘Data discovery’ spotting and querying sensitive data already in user's mailboxes and other DLP(Data Lose Prevention)-like approaches applying control to such data traveling to unsolicited recipients within or without the organization in emails should also feature in your protection armory.
Watch
out for the detection quality vs. false positives ratio.
Of course, it’s also important to avoid ‘false positives’ blocking
legitimate emails in error. Reputable email solutions will have to be subjected
to independent tests, with documented levels of false positives generated
during the performance, so this information should be readily available.

Kaspersky Security for Mail Server: a versatile email security suite offering reliable protection for a broad range of business types and their diverse emailing infrastructures.
Kaspersky Security for Microsoft Office 365: a protection for your cloud-oriented enterprise communication and collaboration apps like Exchange Online, OneDrive, SharePoint Online and Teams from known and unknown cyber-threats.