Contact numbers:
+964 773 157 0666
+964 751 886 5258
+964 780 002 5353
Contact numbers:
+964 773 157 0666
+964 751 886 5258
+964 780 002 5353


Acronis has three research centers to
monitor and investigate cybersecurity incidents around the world. It publishes
the total data and events of this year in a report every year, so let's see
what this report tells us for 2020.
Top 5 numbers in 2020:
1. New fraud techniques appeared by
Covid-19: After the spread of Covid-19 pandemic, people were collecting
information online about how to protect themselves and read the latest news,
and cybercriminals undoubtedly took advantage of this opportunity and used new
scams and tricks to get important and secret information about their victims.
especially using phishing techniques using fake-free test and fake financial
support
2- Remote workers are under attack: The
COVID-19 pandemic has significantly changed the threat landscape, highlighting
numerous security and privacy risks associated with remote work operations –
including remote access to internal company servers, virtual conferencing, and
security training among employees. a number of obstacles and risks arise in
front of the IT team of companies in moving their work environment to a remote
environment or a hybrid environment.
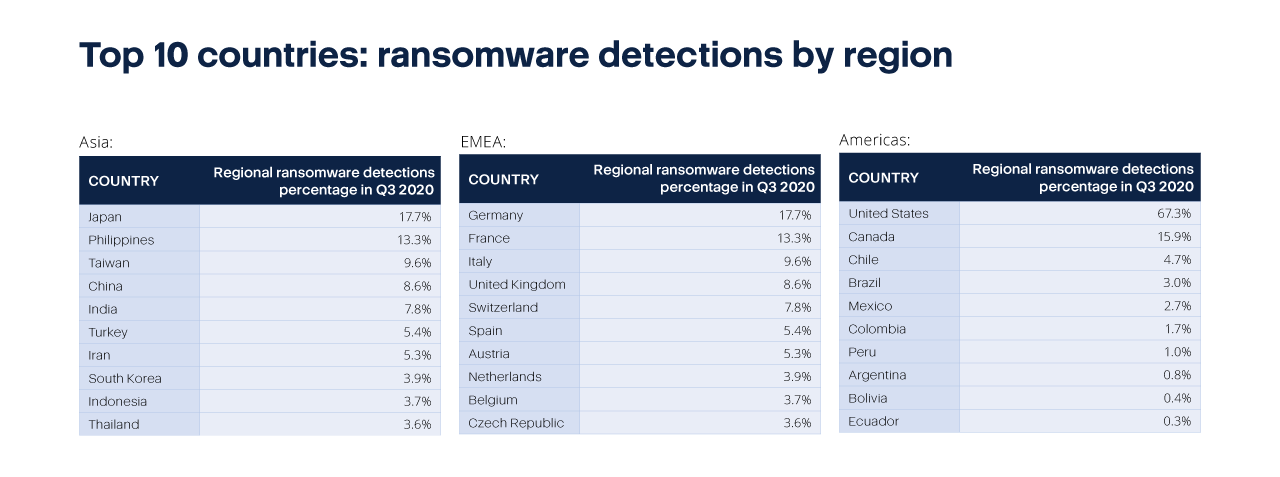
3. Ransomware is still the number one
threat: it is clear that 2020 was The Year of Ransomware, the number of attacks
increased, techniques increased, and the number of victims increased.
4. Simple backup and security are not
enough anymore: since 2016, ransomwares have been attacking backups. cybersecurity
experts have been advising people and companies not to pay the ransom when their files
are encrypted by ransomware instead of that, they should back up their data
and systems because if there is a backup, you don't have to pay to return your
data. But since 2016, many ransomware have also attacked the backups, and they
can stop old model backup programs, as they are unable to protect themselves.
If we take "Conti "
ransomware as an example, the average request for this ransomware is less than
$100,000, using Windows Restart Manager to close any open or unsaved files
before encrypting. It will also delete all hidden backup copies stored on this
COMPUTER, as well as stop all services associated with antivirus, SQL,
cybersecurity, backup programs such as Veeam and BackupExec.