Contact numbers:
+964 773 157 0666
+964 751 886 5258
+964 780 002 5353
Contact numbers:
+964 773 157 0666
+964 751 886 5258
+964 780 002 5353


Cybersecurity is the practice of
protecting critical systems and
sensitive information like computers, servers, mobiles, networks, data, any
device, or electronic system from
digital attacks. It is also called information technology security,
and there are a few common categories in cybersecurity.
Network security: the practice that Strengthens network security for external threats, whether threats are from specific attackers or any regular malware.
Program and application security: focuses on reducing threats on programs, software, and devices. Successful protection starts from the design phase before the program or device deployed.
Cloud security: Protects data in the cloud in storage, while transmitting, and during processing, in order to keep consumer data private.
Information security: Protects data integrity and privacy both in storage and transit.
Operational security: Includes the processes and decisions related to data protection, such as the permissions that users have on the network and system, and determining how and where data is stored and shared according to the security rules.
Business Continuity and Disaster Recovery: Focuses on what organizations do during a cybersecurity incident, or any other incident that causes data loss and work stoppage.
End user education: Focuses on one of the most unpredictable causes of cybersecurity: People (users), at any moment the users can break a protection system by ignoring and breaking the cybersecurity rules of that system. Teaching the user not to open a suspicious link and not use unknown software, and other simple instructions can play an important role in developing an organization's protection system.
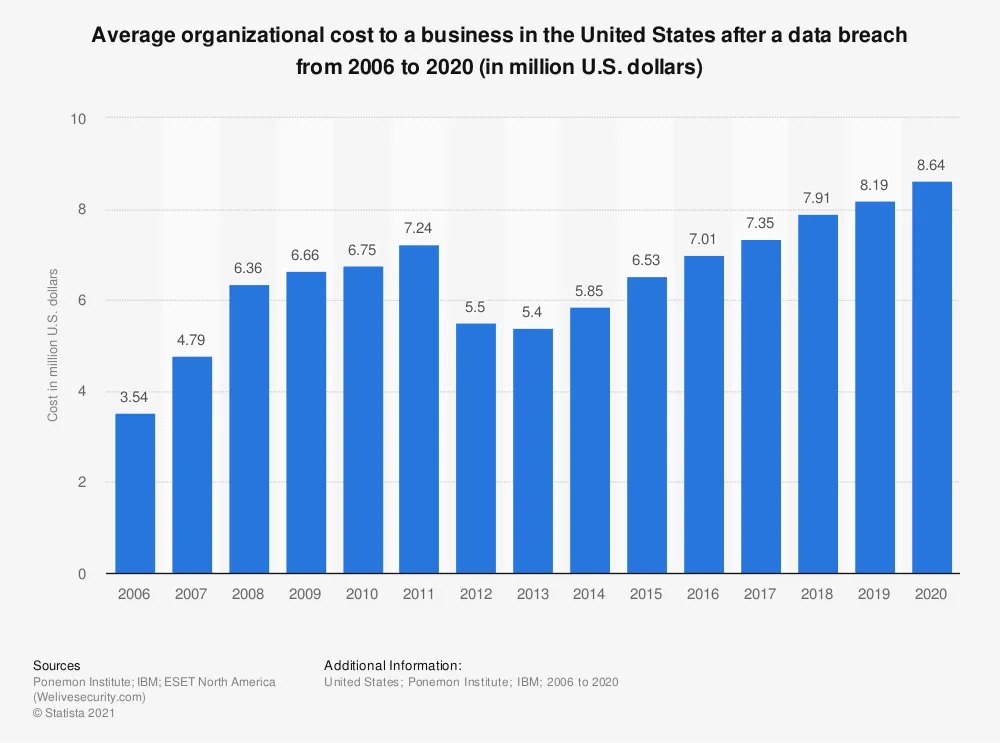
The scale of global cyber threats
continues to grow, the data breaches and hacking of data by cybercriminals is
increasing day by day. In 2020, the average loss of publishing and hacking data
for each event was $ 3.86 million worldwide and in the United States was 8.64
million dollars, these costs include a number of things, such as the cost of
solving and installing new devices and software, the cost of working stoppage
and losing profits, the cost of damage to business and brand reputations. See
the costs of previous years in the chart below.
Some superstitions and
misunderstandings of the cybersecurity world:
Cyber criminals are external: In fact, data leaks are often caused by a harmful person internally, and they may work alone or act as a part of an external hacker group.
The dangers are obvious, and we know them: In fact, the scale of the threats continues to expand, new weaknesses are constantly found in new and old programs and devices, and there is always a chance of human error, in particular, they may leak data because of the neglect of an employee or client, which is one of the reasons why employee education is very important for every organization.
All electronic attack methods are controlled: Cybercriminals are constantly finding new ways to hack, such as Linux systems, accounting technologies, Internet of Things (IoT), devices and cloud environments.
My organization or industry is protected: In fact, all organizations and industries have a significant share in the threats of cybersecurity. Right now, ransomware attacks target all governmental, private sector and non-profit organizations, and their rate is increasing day by day.