Contact numbers:
+964 773 157 0666
+964 751 886 5258
+964 780 002 5353
Contact numbers:
+964 773 157 0666
+964 751 886 5258
+964 780 002 5353


Managing and keeping internal IT operations running smoothly can be time consuming and complicated. With internal IT operations stretched thin, vulnerabilities often go undetected, patches are missed, and your business-critical data could be at risk. By using Avesta Company as your trusted IT service provider, we will focus on proactively protecting your business and handling your IT needs so you can focus on building your business.
Why cyber protection?
As cybercriminals
become more sophisticated in their attacks, it’s getting harder for businesses
to mitigate them. All it takes is one unpatched system, malicious URL, or
malicious file for cybercriminals to gain access to your network, encrypt files,
and deploy ransomware.
While backups are still essential for restoring your data, they’re not enough
to protect your business alone. You need to adopt a comprehensive cyber
protection approach to help mitigate the risks associated with today’s modern
threats.
Is your business at
risk?
The first step to securing your business is knowing where your business is
vulnerable. Our Security Assessment Service can help quantify your exposure, so
we can define the actions we need to take to successfully protect you.
Approach to cybersecurity:
To help keep your
business safe, our protection approach aligns with the National Institute of
Standards and Technology (NIST) framework – a gold standard in the IT security
industry. This helps us protect your business using the industry’s top
guidelines and compliance standards to safeguard you from today’s threats. The
NIST framework consists of five principles: identify, protect, detect,
respond, and recover. Here’s how our cybersecurity approach covers all
five key areas:
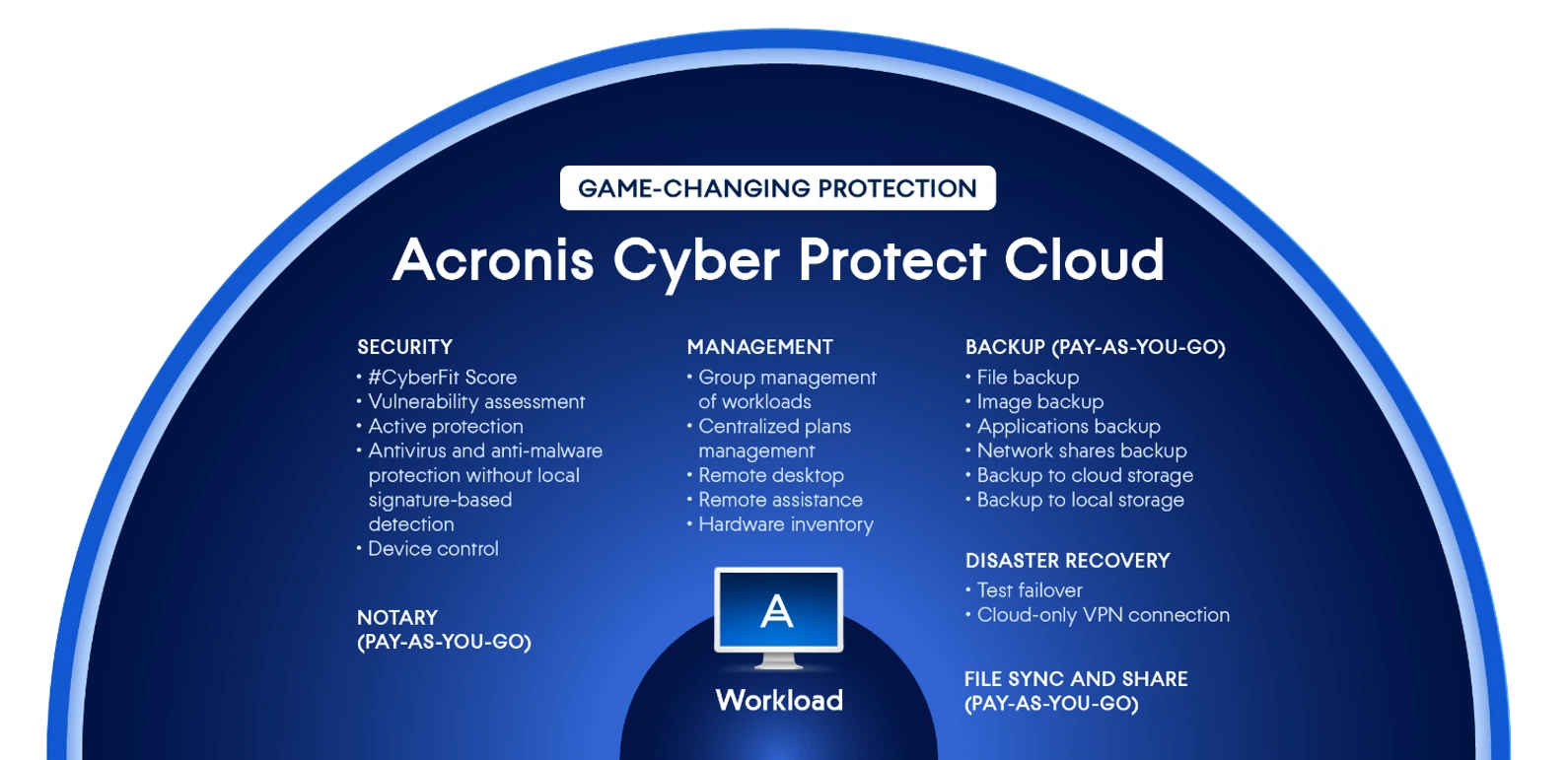
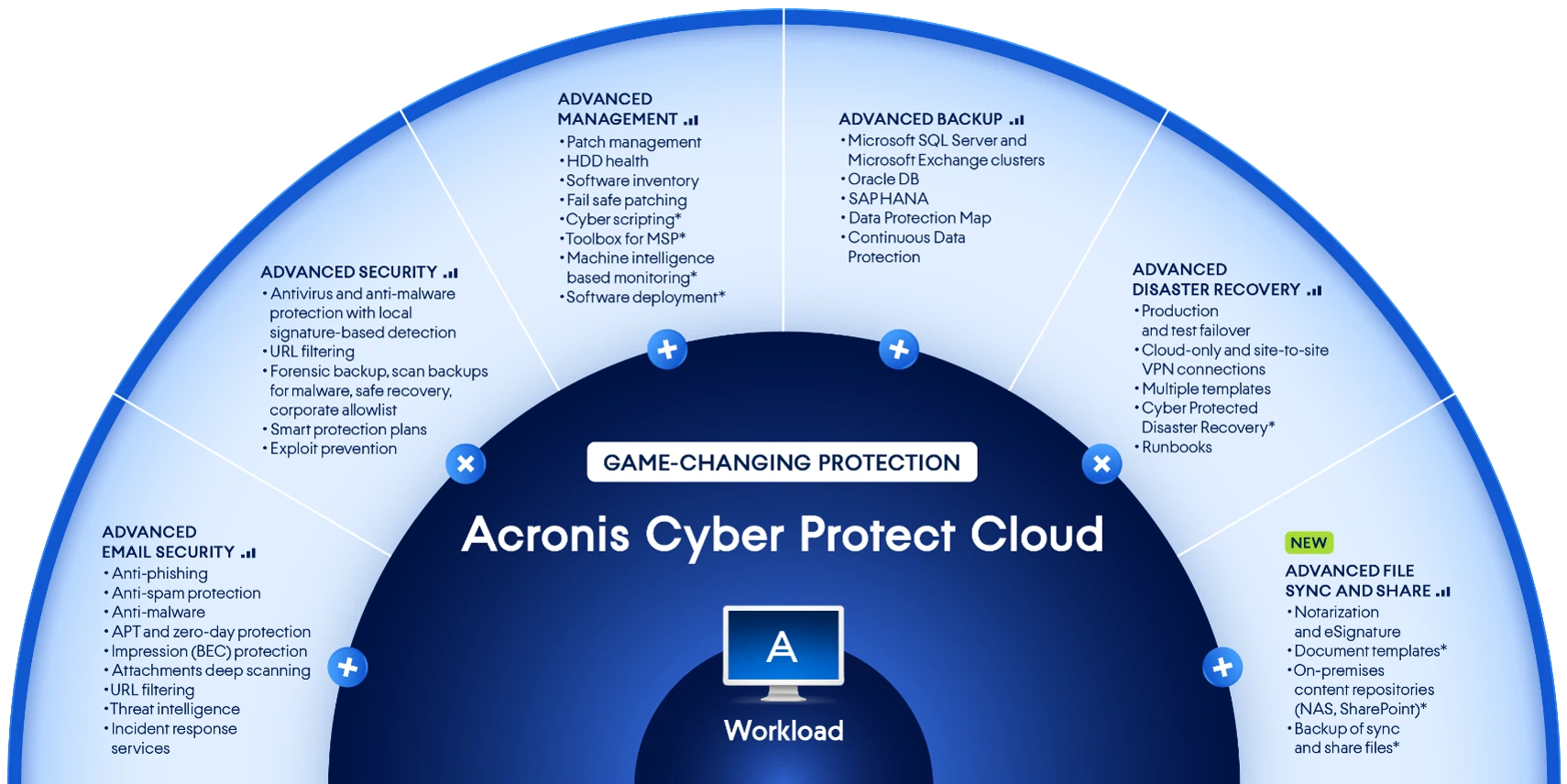
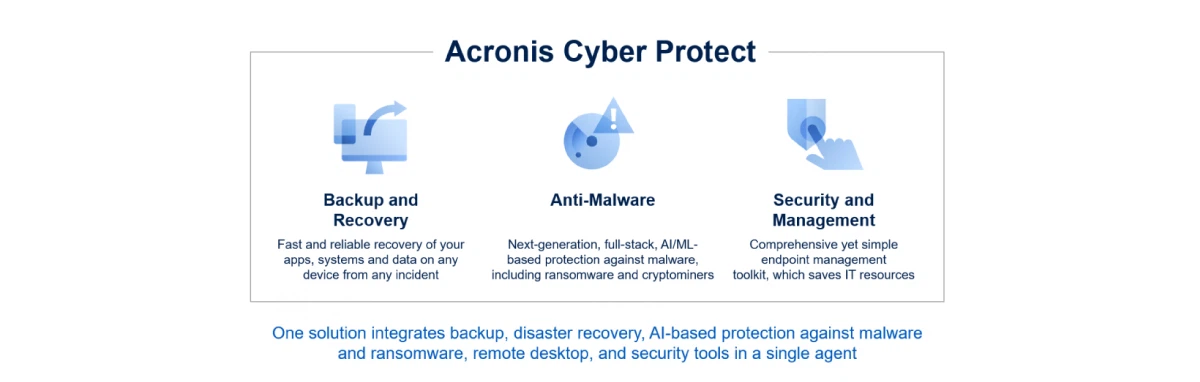
Acronis Cyber Security Cloud includes:
Benefits:
By offering a
proactive approach to cybersecurity, we’re able to provide you:
Advanced Security Packs:
and at the top of the previous solutions there are advanced features like Advanced Backup, Advanced Disaster Recovery, Advanced Management, Advanced Security, etc...